As we’re seeing more and more in technology, identity is everything. It’s what authenticates us against all of the systems we interface with day to day. Having single sign-on (SSO) or same sign-on with 3rd party applications is gaining more and more momentum.
I’ve been working with Azure AD Connect (AAD Connect) since it came into public preview and it’s been a great advancement in authentication synchronization with Office 365 adding support for multi-forest synchronization.
Recently, I ran into an issue/bug within AAD Connect that I was able to resolve with Microsoft. The issue was that password synchronization just stopped working. We updated the AAD Connect install to the latest build (a new iteration was released since the initial install), and then running the script below disabled password synchronization and then re-enabled it, which forces a fresh sync.
Note: For the top variables, it’s case-sensitive. These are the Connector names within the AAD Synchronization Service Manager on the Connector workspace.
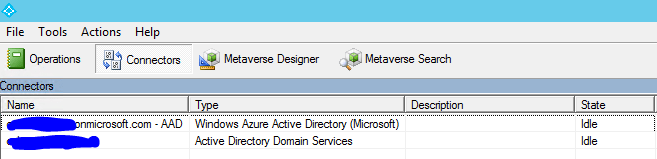
$adConnector = "domain.local"
$aadConnector = "domain.onmicrosoft.com - AAD"
Import-Module adsync
$c = Get-ADSyncConnector -Name $adConnector
$p = New-Object Microsoft.IdentityManagement.PowerShell.ObjectModel.ConfigurationParameter "Microsoft.Synchronize.ForceFullPasswordSync", String, ConnectorGlobal, $null, $null, $null
$p.Value = 1
$c.GlobalParameters.Remove($p.Name)
$c.GlobalParameters.Add($p)
$c = Add-ADSyncConnector -Connector $c
Set-ADSyncAADPasswordSyncConfiguration -SourceConnector $adConnector -TargetConnector $aadConnector -Enable $false
Set-ADSyncAADPasswordSyncConfiguration -SourceConnector $adConnector -TargetConnector $aadConnector -Enable $true
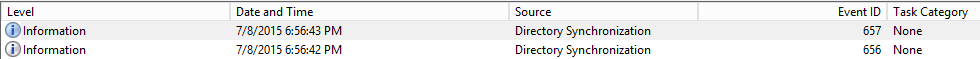
Once you run the script above, you’ll see the following 2 Event IDs showing successful password synchronization. Success!