Zero Trust frameworks are being enhanced by AI automation. In this in-depth guide, we break down how AI in Zero Trust transforms identity, access, and endpoint controls with real-time behavioral analytics, anomaly detection, and self-healing capabilities—without adding enterprise bloat. If you’re an SMB or mid-market leader, you’ll walk away with a pragmatic roadmap you can implement in phases with measurable risk reduction.
- Zero Trust is a strategy, not a single product: never trust, always verify, and assume breach.
- AI-driven automation supercharges Zero Trust with continuous verification, adaptive enforcement, and faster response.
- Start with identity and device trust, then expand to data, apps, and networks—measuring dwell time, MFA coverage, and policy enforcement rates.
- Adopt an AI-enhanced Zero Trust model in three phases: Foundational Hardening → Intelligent Detection → Autonomous Response.
- Build guardrails: governance, model transparency, data minimization, and human-in-the-loop for high-impact actions.
The Role of AI in Zero Trust
At its core, Zero Trust (ZT) reframes access control around the idea that identity, device health, and context determine trust—not the corporate network. Traditional, static policies struggle to keep pace with the complexity and rapid change of modern environments: hybrid identities, remote work, SaaS sprawl, and shadow IT. This is where AI in Zero Trust becomes force-multiplying. Machine learning and automation operationalize the “always verify” mandate by scoring risk in real time, correlating weak signals, and automatically applying the least-privileged action.
AI adds three critical capabilities to any ZT architecture:
- Behavioral baselining and analytics. Models continuously learn what “normal” looks like for users, devices, applications, and service accounts, then surface subtle deviations—such as impossible travel, unusual data access patterns, risky OAuth consent, or emerging persistence techniques.
- Contextual risk scoring. Signals like device posture, geolocation, session tokens, data sensitivity, and attack intelligence feed a continuously updated risk score that drives policy decisions.
- Automated enforcement and response. Based on thresholds, the system can step up authentication, quarantine a device, revoke a token, isolate an endpoint, or rotate a credential—faster than a human queue.
The result is a living Zero Trust fabric that adapts to behavior—not a pile of point tools. For mid-market teams, this means fewer manual triage loops, less alert fatigue, and more reliable containment.
Benefits of Automation in a Zero Trust Model
Zero Trust without automation risks becoming a checklist; with automation, it becomes a system. Here are the tangible outcomes decision-makers should expect:
1) Faster Time to Containment
Automated playbooks shrink mean time to respond (MTTR) from hours to minutes by executing preapproved actions—like forcing password resets, revoking suspicious OAuth grants, or isolating a workstation—directly from detections. This protects revenue by containing lateral movement and stopping data staging early.
2) Precision Access with Continuous Verification
Risk-adaptive access enforces just-in-time and just-enough permissions. When risk rises, the system can require phishing-resistant MFA, push the session to a virtualized browser, or lock access to sensitive repositories until device posture improves. This precision reduces both breach risk and employee friction.
3) Reduced Alert Noise & Analyst Burnout
AI triages and enriches events before analysts see them. Duplicates are suppressed, benign anomalies are closed automatically, and relevant context (asset exposure, user role, data sensitivity, recent threats) is appended. Teams spend more time adjudicating real incidents and less time swatting false positives.
4) Self-Healing Cybersecurity Controls
Automation fixes hygiene drift at scale: re-enables endpoint agents, re-applies baseline GPOs, re-configures logging, revokes stale credentials, and re-enforces conditional access. Systems maintain their secure state rather than waiting for quarterly audits to discover drift.
5) Evidence for Cyber Insurance & Compliance
Insurers increasingly require proof of controls such as MFA, EDR, immutable backups, and privileged access management. Automated Zero Trust provides auditable, timestamped records of policy enforcement and incident response—accelerating underwriting and renewals while reducing premiums over time.
AI-Enhanced Zero Trust Models: A Practical View
Many vendors speak about AI as magic. In practice, an AI-enhanced Zero Trust model looks like a pipeline—signals in, decisions out—with clear checkpoints and safety rails. Below is a pragmatic mental model for SMB and mid-market teams.
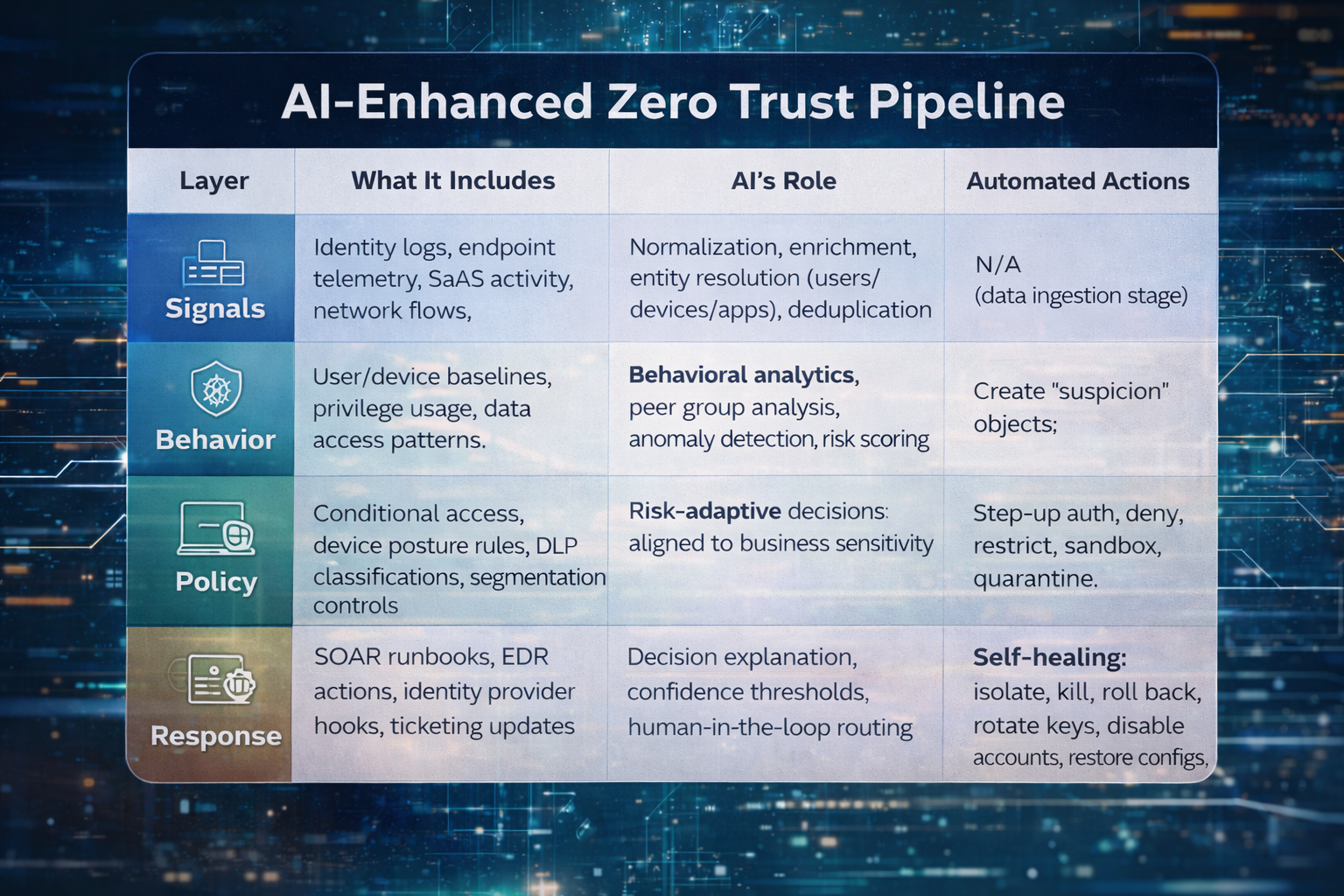
| Layer | What It Includes | AI’s Role | Automated Actions |
|---|---|---|---|
| Signals | Identity logs, endpoint telemetry, SaaS activity, network flows, vulnerability data, threat intel | Normalization, enrichment, entity resolution (users/devices/apps), deduplication | N/A (data ingestion stage) |
| Behavior | User/device baselines, privilege usage, data access patterns | Behavioral analytics, peer group analysis, anomaly detection, risk scoring | Create “suspicion” objects; route to policy engine with context |
| Policy | Conditional access, device posture rules, DLP classifications, segmentation controls | Risk-adaptive decisions aligned to business sensitivity | Step-up auth, deny, restrict, sandbox, quarantine |
| Response | SOAR runbooks, EDR actions, identity provider hooks, ticketing updates | Decision explanation, confidence thresholds, human-in-the-loop routing | Self-healing: isolate, kill, roll back, rotate keys, disable accounts, restore configs |
The key is transparency. Each decision should be explainable: what signals, which baseline deviation, and why the action was taken. This builds trust with security leaders and auditors while enabling targeted tuning.
A Three-Phase Roadmap to AI-Powered Zero Trust
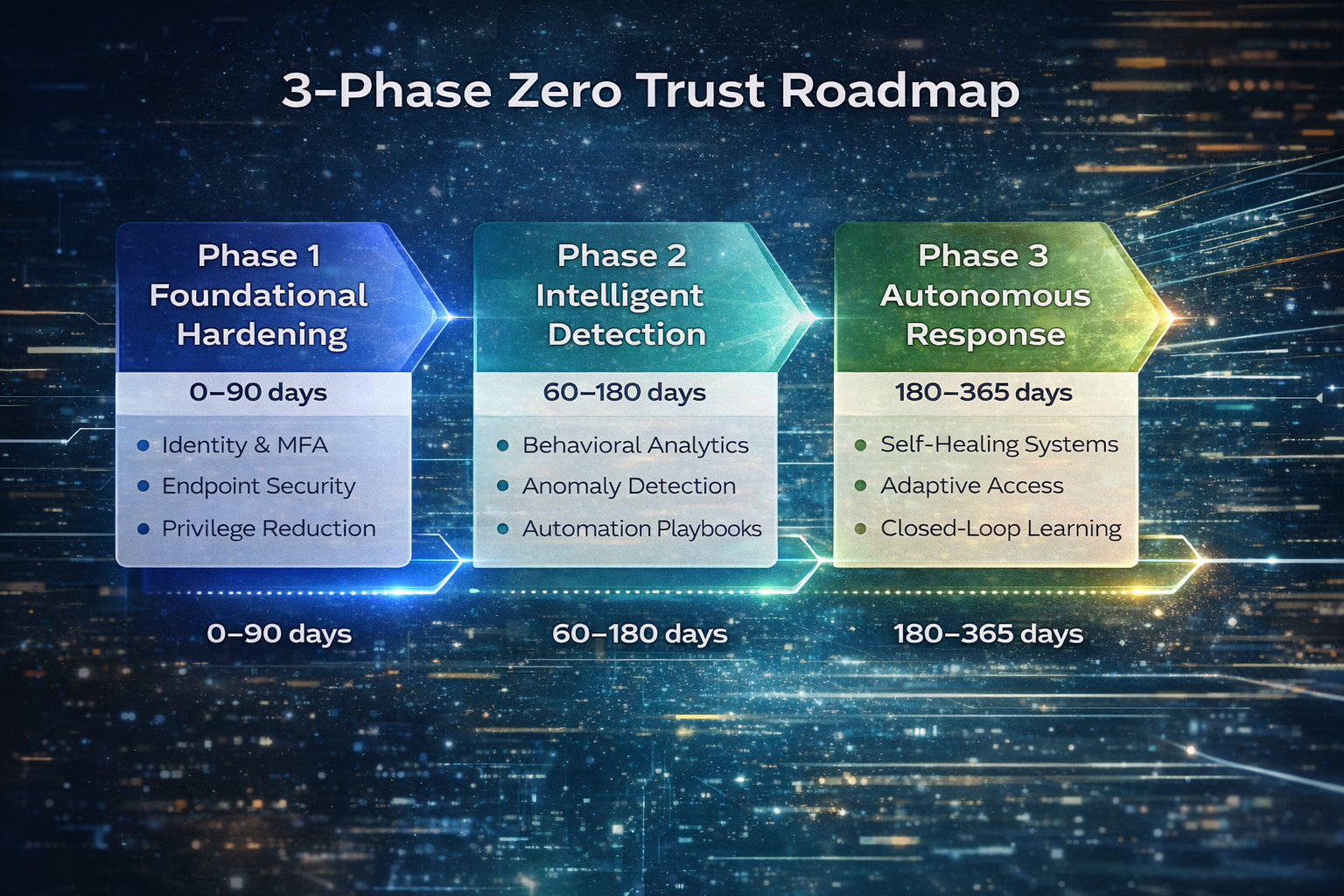
You don’t need a “big bang.” The following roadmap prioritizes quick wins that also lay the foundation for autonomy. You can execute it with your current team by partnering with a managed security provider that brings the platform, runbooks, and 24×7 coverage.
Phase 1: Foundational Hardening (0–90 days)
- Identity First: Enforce phishing-resistant MFA for admins and high-risk roles. Expand to all users with conditional access based on device posture and location.
- Device Trust: Ensure EDR is installed and healthy across endpoints and servers; block outdated OS versions; enforce disk encryption and screen lock.
- Privilege Containment: Eliminate standing admin rights. Implement just-in-time elevation with session recording for IT and third parties.
- Logging & Visibility: Centralize identity, endpoint, and SaaS logs. Enable long-term retention for incident investigations and insurance evidence.
- Backups & DR: Validate immutable backups and recovery time objectives; test restore for critical apps.
Outcome: You’ve created the control surface AI will act upon and the clean data streams it will learn from.
Phase 2: Intelligent Detection (60–180 days)
- Behavioral Analytics: Enable user and entity behavior analytics (UEBA) to baseline normal activity for the workforce and service accounts.
- Anomaly Detection: Turn on detections for impossible travel, unmanaged device access, sensitive data exfiltration, OAuth abuse, and lateral movement chains.
- Risk Scoring: Feed device and identity posture into conditional access: fail-open is eliminated; risky sessions trigger step-up or restrictions.
- Playbook Automation: Automate high-confidence responses (revoke token, block sign-in, quarantine endpoint) with human review for medium-confidence events.
Outcome: Analysts shift from chasing alerts to supervising decisions. MTTR drops; attack surface shrinks.
Phase 3: Autonomous Response (180–365 days)
- Self-Healing Configurations: Automatically re-enable agents, re-enforce baseline security settings, and rotate keys/secrets when drift or compromise is detected.
- Adaptive Access: Use continuous signals to adjust privileges in-session—restricting downloads, enabling read-only access, or requiring re-authentication for sensitive actions.
- Closed-Loop Learning: Outcomes of investigations train models; false positives decrease; playbooks refine themselves via change control.
- Business Integration: Map controls to critical workflows (finance, sales, manufacturing) to optimize productivity while maintaining protection.
Outcome: Zero Trust becomes the operational fabric of your security program—predictive, precise, and resilient.
Key Controls: Behavioral Analytics, Anomaly Detection, & Self-Healing
To translate strategy into operations, focus on three control categories that deliver the most value for effort. These align directly with the secondary keywords we’re targeting and are feasible for mid-market teams.
Behavioral Analytics
Behavioral analytics compares entities to themselves and their peers. Rather than static rules (“block all access from X”), it asks, “Is this activity normal for this user/device/application?” Practical examples include:
- Detecting a salesperson who suddenly pulls thousands of records from a finance SaaS she rarely touches.
- Flagging a server account that begins interactive logons or scripts for new administrative shares.
- Spotting an endpoint that reaches out to an unusual set of IPs or new Tor exit nodes at 3 a.m.
When paired with sensitivity labels and data classification, behavioral analytics can prioritize alerts involving regulated or crown-jewel data sets.
Anomaly Detection
Anomaly detection is the early-warning system. It identifies outliers—rare OAuth consent scopes, atypical egress volumes, or forged MFA prompts—and correlates them across identity, endpoint, and SaaS. Modern systems reduce noise by enriching anomalies with asset criticality and recent change windows (for example, distinguishing a legitimate new admin tool rollout from malicious persistence).
Self-Healing Capabilities
The most underrated benefit of automation is the ability to repair security controls at machine speed:
- Re-installing or restarting a failed EDR sensor and confirming heartbeat before allowing the device back on the network.
- Rolling back malicious registry changes or unauthorized scheduled tasks.
- Rotating tokens and keys after suspicious behavior without waiting for a change board cycle.
- Auto-quarantining files and restoring from a last-known-good snapshot after ransomware behavior is detected.
Self-healing not only limits dwell time; it frees analysts to focus on novel threats, red team exercises, and improving the program rather than firefighting.
Reference Architecture: AI + Zero Trust Without the Bloat
Most organizations already own 60–70% of the components required for AI-powered Zero Trust—identity provider, EDR, email security, and some logging. The goal is to integrate rather than rip and replace. Here’s a lean reference stack:
- Identity & Access: A modern identity provider with conditional access, risk-based policies, phishing-resistant MFA, and SCIM provisioning. Integrate privileged access management (PAM) for admin workflows.
- Endpoint & Server: An EDR/XDR platform capable of real-time telemetry, isolation, rollback, and API-driven actions.
- Email/SaaS Security: Advanced phishing protection, OAuth monitoring, DLP controls, and tenant-to-tenant anomaly visibility.
- Data Security: Classification, sensitivity labels, encryption, and just-in-time access to critical repositories.
- Telemetry & Analytics: A centralized log platform with UEBA and detection content mapped to MITRE ATT&CK—plus a SOAR layer to automate responses.
- Governance & Change: Policy-as-code, approvals for high-impact actions, version-controlled playbooks, and evidence capture for audits and insurers.
The connective tissue is automation. Use APIs and webhooks to ensure your identity provider, EDR, SaaS platforms, and SOAR exchange risk signals and execute decisions without human bottlenecks.
How to Measure Success & Prove It
Leaders need quantifiable outcomes for boards, insurers, and auditors. Track:
- Mean Time to Respond (MTTR): target <30 minutes for high-confidence detections with automated actions.
- EDR Coverage & Health: >98% of endpoints reporting and protected; <24h mean time to remediate sensor failures.
- MFA & Conditional Access Coverage: 100% for admins, >95% for workforce; device posture enforcement for all privileged workflows.
- Privilege Utilization: reduction in standing admin accounts; percent of elevated sessions approved and recorded.
- Policy Enforcement Rate: percentage of risky sessions receiving step-up, deny, or sandbox action.
- Backup Integrity: verified restore tests for critical apps at least quarterly.
Present these as a dashboard tied to business risk: “hours of exposure avoided,” “incidents auto-contained,” and “recoveries validated.” This reframes security as a performance function rather than a cost center.
Governance & Guardrails for Responsible AI
Autonomy without governance is risky. Before enabling fully automated actions, establish:
- Decision Transparency: Require human-readable rationales for enforcement actions, with links to the signals and baselines considered.
- Confidence Thresholds: Automate only when confidence is high, and impact is low; route medium confidence to analyst review; escalate high-impact actions to an on-duty approver.
- Change Control: Treat playbooks as code with versioning, peer review, and rollback procedures.
- Data Minimization: Retain only necessary personal data; apply retention and masking consistent with privacy regulations.
- Red Teaming & Model Validation: Simulate attacks to test model drift and false-negative risk; continuously recalibrate.
With these guardrails, you gain the speed of automation without sacrificing oversight or compliance.
High-Impact Use Cases You Can Automate Today
- Account Takeover (ATO) Containment: Detect impossible travel and atypical MFA push patterns; automatically revoke active tokens, require phishing-resistant MFA, and notify the user via secure channel.
- Privileged Misuse: Block elevation if device posture is noncompliant; force session recording; auto-expire elevated access after the approved task completes.
- Ransomware Behavior: Monitor encryption-like file events and suspicious PowerShell activity; isolate the endpoint, kill processes, and trigger automatic snapshot restore.
- Data Exfiltration from SaaS: Detect unusual downloads from sensitive SharePoint or CRM systems; switch to read-only mode and require manager approval for exports.
- Shadow IT & OAuth Abuse: Flag risky third-party app consents; auto-revoke and notify the requester with a sanctioned alternative.
Common Obstacles & How to Get Past Them
“Our data is too messy for AI.”
Start with the signals that matter most—identity and endpoint—then expand. Normalize fields, map identities to devices, and enrich with asset criticality. You don’t need perfect data to get meaningful wins; you need consistent data from the core systems.
“We can’t afford a data science team.”
You don’t need one. Use platforms with built-in UEBA and detection packs, then layer in a managed detection and response (MDR) partner that tunes models for your environment. Reserve in-house expertise for governance and exception handling.
“What if automation blocks the CEO?”
Implement graduated responses. For high-risk roles, favor step-up challenges and session sandboxing over hard denies unless risk is unequivocal. Maintain 24×7 escalation paths and break-glass accounts with out-of-band controls.
“We’re a Microsoft/Google/Splunk shop—will this work?”
Yes. The principles are vendor-agnostic. What matters is API access, policy hooks, and the ability to enrich and act across identity, endpoint, and SaaS. A good partner will integrate with your existing investments rather than rip them out.
Cost & ROI: What Mid-Market Teams Should Expect
Budget holders need clean numbers. While every environment differs, you can forecast costs in three buckets—platform, services, and change management—and map them to measurable returns.
Typical Cost Drivers
- Platform Licensing: Identity provider tiers with conditional access and risk-based policies; EDR/XDR; log analytics/UEBA; SOAR. For a 500–1,500-user org, this commonly ranges from low to mid six figures annually if starting from near zero. Many clients already own 60–70% of the stack through enterprise suites, reducing net-new spend.
- Implementation & Tuning: One-time services to deploy policies, baselines, and playbooks; integration with ticketing and ITSM; evidence/reporting setup for insurance and audits.
- MDR/Co-Managed Operations: 24×7 monitoring, triage, and guided or automated response; continuous detection content updates; quarterly tabletop exercises.
- Change Management: Communication, training for admins and users, and exception handling (e.g., legacy apps that struggle with modern auth).
Return on Investment
Quantify ROI by connecting controls to avoided losses and operational savings:
- MTTR Reduction: Cutting containment time from 8 hours to 30 minutes prevents data staging and stops ransomware from expanding its blast radius—translating directly into avoided downtime and fewer paid ransoms.
- Analyst Efficiency: Automation that closes 40–60% of benign alerts reduces overtime and reliance on contractors, enabling a leaner team to cover more assets.
- Insurance & Compliance: Demonstrable controls can reduce premiums and accelerate claims/renewals; audit prep time drops when evidence is produced automatically by the system.
- Fewer Incidents Escalated: Risk-adaptive access halts many events at the first step (token revocation, step-up auth), so they never require full incident handling.
If a mid-market org experiences two moderate incidents per year causing 24 hours of disruption each, and automation reduces disruption to 6 hours, the reclaimed 36 hours across 500 employees at an average fully loaded $70/hour equals ~$1.26M in productivity preserved—before considering reputational harm, legal costs, or ransom exposure.
Case Study: 1,200-User Manufacturer Cuts MTTR by 87%
Background: A multi-site manufacturer with legacy on-prem AD, a growing SaaS footprint, and a small IT team (five admins, two security generalists). They faced alert fatigue, uneven MFA coverage for contractors, and frequent EDR health drift.
Approach
- Phase 1—Hardening: Rolled out phishing-resistant MFA to all admins and high-risk roles; enforced device posture checks; closed local admin rights; validated immutable backups for ERP and MES systems.
- Phase 2—Detection: Enabled UEBA across identity, endpoints, and Microsoft 365; built playbooks for ATO, EDR tamper, and sensitive data egress; integrated SOAR with ITSM for approvals and evidence.
- Phase 3—Autonomous Response: Approved automated revocation of suspicious sessions, forced re-auth with FIDO2, and endpoint isolation on ransomware behavior; enabled self-healing for EDR sensors.
Outcomes (First 6 Months)
- MTTR: Dropped from 3.9 hours average triage/containment to 30 minutes for high-confidence incidents—an 87% improvement.
- Coverage: EDR health moved from 91% to 99% with self-healing; MFA coverage reached 100% for admins and 97% for the workforce, including contractors.
- Alert Volume: 52% of alerts were closed automatically with enrichment and suppression; analysts focused on 14 weekly “priority” investigations instead of 60+ raw alerts.
- Audit Evidence: Insurance renewal completed in 11 days (down from 5 weeks) with generated enforcement logs and tabletop test reports.
Business impact: A phishing-based credential theft led to a suspicious cloud session outside business hours. The system revoked tokens, challenged with FIDO2, blocked risky OAuth scopes, and opened a case with evidence. No data exfiltration occurred; production never paused; leadership received a same-day after-action report tied to KPIs.
Buyer’s Guide: Evaluating AI-Driven Zero Trust Platforms
There’s no shortage of marketing claims. Use these criteria to separate signal from noise:
- Integration Depth: Native hooks for your identity provider, EDR/XDR, email/SaaS suite, data classification, and ticketing. Ask for proof: APIs used, actions supported, and rate limits.
- Explainability: Every automated decision should include a clear rationale and links to underlying telemetry.
- Policy-as-Code: Version control, peer review, and easy rollback for detection content and playbooks.
- Confidence Controls: Granular thresholds for when to auto-act, require step-up, or route for approval.
- Self-Healing Library: Built-in remediations for agent health, logging, and common configuration drift.
- Evidence & Reporting: Out-of-the-box reports aligned to insurance questionnaires and common frameworks.
- Services Model: Can your team co-manage? Is 24×7 coverage available? Are tuning workshops included?
- Total Cost Ownership: Clarify what’s included in each license tier and where you’ll incur add-on ingestion or automation fees.
Implementation Risks & How We Mitigate Them
Legacy Applications & Modern Authentication
Risk: Older apps may not support modern auth or device posture checks.
Mitigation: Place them behind identity-aware proxies, segment network access, and assign temporary exceptions with compensating controls and a retirement plan.
Automation Misfires
Risk: Overly aggressive rules can interrupt critical workflows.
Mitigation: Start with observe mode → soft actions (session revocation, step-up auth) → restricted automation for low-impact cases. Maintain break-glass procedures and 24×7 approvers.
Alert Blind Spots
Risk: Missing telemetry reduces detection quality.
Mitigation: Institute “no dark assets” policies, automated onboarding checks for new devices and users, and weekly coverage reports to operations leadership.
Change Fatigue
Risk: User friction during MFA rollouts and posture enforcement.
Mitigation: Clear comms, tiered deployment, quick “why this matters” training, and alternate methods for legitimate travel or offline scenarios.
Quick Glossary
- UEBA: User and Entity Behavior Analytics; models that learn “normal” behavior to surface anomalies.
- SOAR: Security Orchestration, Automation, and Response; playbooks that automate actions across tools.
- Risk-Adaptive Access: Policies that change access in real time based on risk signals and context.
- Self-Healing: Automated actions that restore security baselines (agents, configs, keys) without manual intervention.
Why Cyber Advisors: Proven Partnerships Across Industries & Non-Profits
From 50-seat nonprofits to multi-site manufacturers and healthcare systems, Cyber Advisors has partnered with organizations of every size and mission to design, implement, and operate AI-enhanced Zero Trust programs that fit real-world constraints. Our co-managed model meets you where you are—augmenting your team with 24×7 detection and response, policy engineering, and automation runbooks—so you gain enterprise-grade outcomes without enterprise bloat. We bring deep experience across regulated and resource-constrained environments alike, aligning controls to your business workflows, budget, and compliance needs. If you’re ready to turn strategy into day-to-day results, we’re ready to help.
Next Steps: Partner with Cyber Advisors to Integrate AI-Driven Automation
AI-driven automation enhances Zero Trust by turning policy into practice—continuously and at machine speed. Whether you’re securing a distributed workforce, protecting regulated data, or preparing for a cyber insurance renewal, our team can help you design and operate a right-sized program that delivers outcomes, not just dashboards.
Schedule a 30-Minute Zero Trust Automation Consult
- Map current tools to a lean, AI-enhanced Zero Trust architecture.
- Identify 2–3 quick-win playbooks for automated containment.
- Get a 90-day plan with metrics, approvals, and evidence capture.




