Manufacturing leaders have never had more pressure to keep production running while defending against ransomware, supply chain compromise, and targeted attacks on operational technology (OT). The challenge is that “cyber maturity” in manufacturing isn’t a single product you buy—it’s a coordinated set of manufacturing cybersecurity tools, processes, and OT security services that protect both IT and OT without disrupting uptime.
In this guide, we’ll walk through the essential tools, services, and best practices manufacturers need to reach cyber maturity—from SCADA security and network segmentation to vendor risk management and patch management. We’ll also share practical implementation advice and examples of what “good” looks like in real environments.
Quick definition: Cyber maturity is the ability to consistently prevent, detect, respond to, and recover from cyber threats across both IT and OT—while maintaining safety, quality, and uptime.
Why Cyber Maturity in Manufacturing Is Different
Manufacturing environments differ from typical office networks because they rely on long-lived systems, specialized industrial protocols, and equipment that cannot be casually rebooted or patched. Safety considerations and production schedules add complexity: what’s acceptable downtime in IT might be unacceptable in OT.
Many manufacturers also operate with a mix of legacy controllers, newer Industrial IoT devices, third-party remote access, and multiple sites—all connected by a supply chain of vendors and integrators. In this reality, cyber maturity requires:
- Visibility into IT and OT assets, communications, and risk.
- Segmentation to prevent small incidents from becoming plant-wide outages.
- Detection built for industrial protocols and abnormal process behavior.
- Response and recovery plans that preserve safety and operational continuity.
- Governance that aligns engineering, operations, and IT around a shared playbook.
The goal is not to turn plants into “perfectly secure” environments (that’s not realistic). The goal is to ensure your business can withstand the most likely attacks with minimal disruption—and that you can prove control maturity to customers, insurers, auditors, and regulators.
The Core Tool Stack for Cyber Maturity in Manufacturing

Think of this as a layered defense model that scales from a single plant to multi-site operations. Some manufacturers already own parts of this stack but lack OT integration or coverage. Others have OT coverage but weak governance, vendor oversight, or recovery capability. Mature programs typically address each of the categories below.
| Capability | What It Does | Why It Matters in OT/Manufacturing |
|---|---|---|
| Asset Visibility | Discovers and inventories devices, software, and data flows. | You can’t protect what you can’t see—especially unmanaged OT endpoints. |
| SCADA/ICS Security | Monitors industrial protocols and controller behavior for anomalies. | Traditional IT tools lack process-level indicators and ICS-specific threat detection. |
| Network Segmentation | Separates zones and controls lateral movement. | Limits blast radius and helps keep production running during incidents. |
| Patch & Vulnerability Management | Prioritizes vulnerabilities and coordinates safe remediation. | OT patching requires scheduling, testing, and compensating controls. |
| Vendor Risk Management | Assesses and governs third-party access and security posture. | Remote vendors can become a direct pathway into your plant network. |
| Detection & Response Services | 24/7 monitoring, triage, and incident response support. | Manufacturers need a rapid response to contain threats without disrupting safety. |
Next, we’ll break down the tools and services in each category, including best practices and examples.
1) SCADA/ICS Security: Tools Built for Industrial Reality
SCADA security and broader ICS security focus on systems that control physical processes, including PLCs, HMIs, SCADA servers, historians, engineering workstations, and the industrial networks that connect them. The purpose is to detect abnormal behavior that may indicate compromise without installing risky agents on fragile devices.
What “Good” SCADA/ICS Security Covers
- Passive network monitoring that understands industrial protocols (for example, Modbus, DNP3, EtherNet/IP, Profinet, OPC).
- Asset discovery and mapping of controllers, IO devices, and OT endpoints across zones.
- Baseline behavioral analytics for normal process communications and deviations.
- Alerting tuned for OT (changes to ladder logic, unauthorized engineering access, suspicious remote sessions).
- Integration with IT security tooling (SIEM, SOAR, ticketing) to create a single response workflow.
Tools Manufacturers Commonly Use
Mature programs typically combine a dedicated OT visibility platform with controls that limit access and enforce safe operations. Depending on the environment, tool categories include:
- OT network detection and response (OT NDR) for continuous monitoring and threat detection.
- Industrial intrusion detection that identifies protocol misuse and suspicious commands.
- Secure remote access solutions for vendors and integrators, with session control and audit trails.
- Configuration and change monitoring for critical OT systems and engineering workstations.
Best Practices That Improve Outcomes Fast
- Start with visibility at the plant boundary and key control zones. You’ll gain immediate insight into assets and risky communications.
- Prioritize detection use cases with operational impact: ransomware propagation, unauthorized remote access, and unsafe setpoint changes.
- Align alerts with response playbooks so engineering and IT know what to do when a signal is triggered.
- Feed findings into segmentation and patch planning—visibility is only valuable if it drives action.
Practical tip: In many plants, you can improve OT security substantially without touching PLCs. Passive monitoring, segmentation, and controlled remote access often deliver the biggest risk reduction with the least operational friction.
2) Network Segmentation: The Foundation of OT Resilience
If cyber maturity in manufacturing had a “single best investment,” many practitioners would argue it’s segmentation. When segmentation is done well, incidents don’t become outages. When it’s missing, a compromise of one endpoint can quickly spread to production servers, engineering workstations, and plant-floor operations.
Segmentation Goals in Manufacturing
- Control lateral movement between IT and OT and between OT zones.
- Protect safety systems and critical controllers with strict access rules.
- Reduce the blast radius of ransomware and credential theft.
- Support remote access without opening broad network pathways.
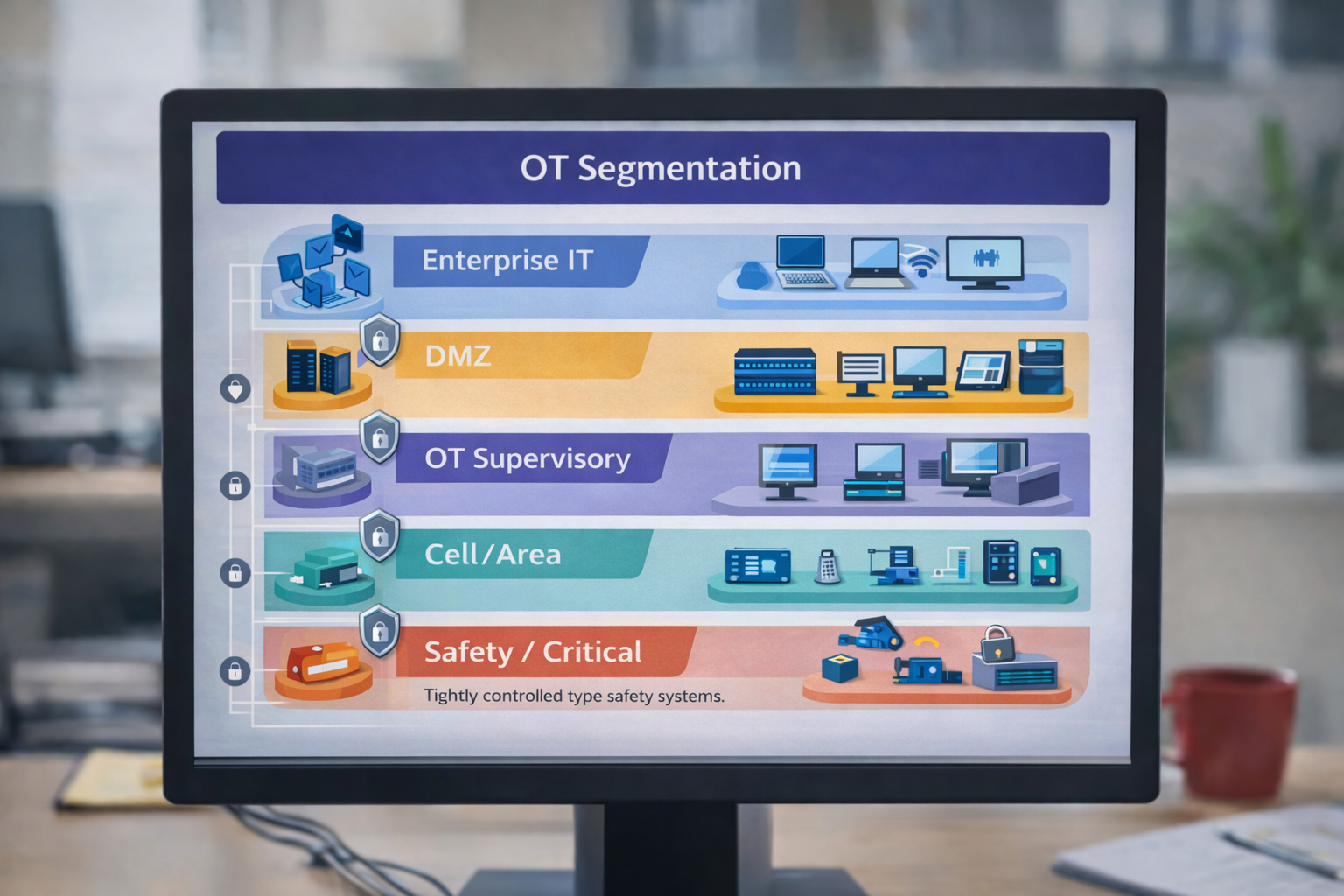
Common Segmentation Models
Many manufacturers align with proven zoning concepts (often reflecting ISA/IEC 62443 principles), including:
- Enterprise IT (business systems, email, ERP).
- DMZ (data brokers, historians replication, jump servers, patch staging).
- OT Supervisory Zone (SCADA servers, HMIs, engineering workstations).
- Cell/Area Zones (line-specific controllers, machines, IIoT devices).
- Safety / Critical Systems (most restricted, tightly controlled).
Tools & Controls That Enable Segmentation
- Industrial firewalls are designed for OT traffic and harsh environments.
- Network access control (NAC) for identifying devices and enforcing policy where feasible.
- Microsegmentation to isolate workloads and restrict communications at a granular level.
- Secure jump servers and application-level gateways for remote management tasks.
- Data diodes / unidirectional gateways where one-way data flow is needed for safety or compliance.
Case Study Pattern: “From Flat to Zoned”
A common maturity leap occurs when a plant moves from a flat network to defined zones with a controlled DMZ. The early wins are fast: fewer pathways for ransomware, clearer remote access flows, and the ability to isolate parts of the network during maintenance or an incident.
The key is to implement segmentation in a way that respects operations. Start by mapping communications, then enforce policy in stages—monitoring first, blocking later, and validating with operations stakeholders before tightening controls.
3) Vendor Risk Management: Protecting the Plant Perimeter You Don’t Control
Manufacturers rely on vendors for OEM equipment, automation integration, maintenance, and remote troubleshooting. Unfortunately, vendors can also introduce risk through shared credentials, unmanaged laptops, insecure remote tools, and inconsistent security practices. A mature program treats vendor access as a high-value threat pathway and builds governance around it.
What Vendor Risk Management Looks Like in Manufacturing
- Vendor inventory with clarity on who has access to what, why, and when.
- Access controls that enforce least privilege and remove access when no longer needed.
- Security requirements baked into contracts and onboarding (MFA, logging, patching expectations).
- Continuous monitoring of remote sessions and privileged activity.
- Periodic reassessments based on criticality (more scrutiny for vendors touching production systems).
Tools & Services That Strengthen Vendor Oversight
- Third-party risk management (TPRM) platforms to track questionnaires, evidence, and risk scoring.
- Privileged access management (PAM) to secure admin credentials and session usage.
- Secure remote access solutions that provide session recording, approvals, and time-bound access.
- Identity and access management (IAM) with MFA and role-based access control.
Best Practices for Vendor Access in OT
- Eliminate shared accounts wherever possible; use named identities tied to individuals.
- Use just-in-time access for remote maintenance instead of always-on VPNs.
- Route vendor access through controlled chokepoints (jump boxes, gateways) with monitoring.
- Log everything and retain remote access records to support investigations and compliance.
- Practice offboarding—removing access cleanly is just as important as granting it.
4) Patch Management: The Most Misunderstood Discipline in OT
In IT, patching is often routine: deploy updates, reboot if needed, and move on. In OT, patching must account for operational constraints, vendor validation, safety, and the risk of downtime. That doesn’t mean you ignore patching— it means you build a patch and vulnerability program designed for the plant.
What Effective OT Patch Management Includes
- Asset and version awareness (OS versions, firmware, application builds, controller versions).
- Vulnerability intake (vendor advisories, ICS CERT notices, threat intelligence).
- Risk-based prioritization based on exposure and operational impact—not just CVSS scores.
- Test and staging process to validate patches before production deployment.
- Maintenance window planning aligned to production schedules.
- Compensating controls when patching isn’t feasible (segmentation, allowlisting, strict remote access, monitoring).
Tools Manufacturers Use for OT-Aware Vulnerability Management
Mature organizations use a combination of:
- Passive OT asset discovery to identify systems and software without disrupting operations.
- Vulnerability management platforms with OT context and safe scanning methods (where supported).
- Patch orchestration tools for IT systems and carefully controlled approaches for OT systems.
- Configuration management to track baselines and detect drift over time.
Best Practices: Patching Without Breaking Production
- Segment first to prevent unpatched systems from being directly exposed to broad network traffic.
- Patch the “bridges” aggressively (jump servers, remote access gateways, DMZ systems, domain controllers).
- Use an OT patch committee that includes IT security, engineering, and operations to approve and schedule changes.
- Track exceptions with an owner, rationale, compensating controls, and a revisit date.
Reality check: Cyber maturity isn’t “everything patched instantly.” It’s “we understand our exposure, we prioritize what matters, and we reduce risk through patching and compensating controls.”
Beyond the Big Four: Additional Tools & Services That Drive Maturity
SCADA/ICS security, segmentation, vendor oversight, and patch management are core. But most mature manufacturers round out their programs with complementary capabilities that improve prevention, detection, and recovery.
Asset Inventory & Configuration Management
If your asset list is a spreadsheet updated annually, your cyber maturity will remain out of reach. You need reliable visibility into what exists, where it lives, how it connects, and who owns it. This is especially critical in OT, where “shadow devices” appear during maintenance, expansions, or vendor work.
- IT tools: endpoint management, CMDB, software inventory, device compliance reporting.
- OT tools: passive discovery, topology mapping, controller identification, firmware awareness.
- Outcome: faster incident response, better patch planning, clearer segmentation decisions.
Identity Security: MFA, PAM, & Least Privilege
Many plant incidents start with credentials—phished accounts, reused passwords, shared admin logins, or overly broad access. Identity controls reduce this risk dramatically.
- Multi-factor authentication (MFA) for remote access, admin actions, and critical systems.
- Privileged access management (PAM) to control admin credentials, enforce approvals, and record sessions.
- Role-based access aligned to job function and operational need.
- Service account governance to reduce “invisible” privileged pathways.
Endpoint Security for IT & OT-Adjacent Systems
While you may not install agents on PLCs, many OT environments include Windows workstations, servers, and engineering machines that can run endpoint protection. Mature programs typically use:
- Endpoint detection and response (EDR) on servers and workstations in OT supervisory zones (where validated).
- Application allowlisting on critical systems to prevent the execution of unauthorized executables.
- Device control to manage USB usage and reduce pathways for malware introduction.
The best results occur when endpoint tooling is coordinated with operations and tested carefully—especially for systems that interface with production lines.
Network Detection & Centralized Logging (SIEM)
Cyber maturity improves when IT and OT signals converge into a single view. This typically involves:
- SIEM to aggregate logs from firewalls, servers, endpoints, identity, and OT monitoring platforms.
- Use-case tuning specific to manufacturing: suspicious remote access, lateral movement, abnormal protocol use, and ransomware behaviors.
- Automated triage and ticketing to reduce alert fatigue and speed response.
Managed Detection & Response (MDR) and 24/7 SOC Services
Many manufacturers don’t have internal teams to monitor and respond around the clock—especially when you consider the specialized expertise required to interpret OT signals. OT security services often include:
- 24/7 monitoring for IT and OT events.
- Threat hunting and proactive validation of suspicious activity.
- Incident response coordination that aligns IT containment with operational safety.
- Continuous improvement via monthly reporting, roadmap recommendations, and control tuning.
Backup, Disaster Recovery, & Ransomware Resilience
Recovery is a core pillar of maturity. If ransomware hits, you need confidence that you can restore operations quickly. For manufacturing, this involves more than backing up files—it involves restoring critical servers, ensuring configuration integrity, and validating that production can resume safely.
- Immutable backups and protected storage to reduce the chance that backups are encrypted or deleted.
- Regular restore testing (tabletop + technical) to ensure backups actually work.
- Priority-based recovery plans that identify the “must restore first” systems.
- Offline copies of critical controller configurations and engineering project files.
Security Awareness & OT-Specific Training
Training matters because manufacturing is a people-driven environment—maintenance, engineering, operations, IT, and vendors each influence risk. Mature programs provide:
- Phishing resistance and practical training for office users.
- Role-based training for engineers and maintenance on safe remote access, removable media, and incident reporting.
- Operational drills that simulate ransomware or OT disruptions to validate readiness.
Services Manufacturers Need to Tie the Tools Together
Tools alone rarely deliver maturity. The manufacturers that progress fastest pair technology with services that create alignment, governance, and repeatable execution.
OT/IT Risk Assessment & Roadmap
A structured assessment helps you prioritize investments and avoid spending money on tools that don’t reduce operational risk. A good roadmap typically includes:
- Current-state visibility: asset coverage, segmentation gaps, remote access paths, critical vulnerabilities.
- Operational risk ranking: what could stop production, cause safety issues, or create major financial loss?
- Phased plan: quick wins, 6–12 month initiatives, and longer-term modernization goals.
Architecture & Implementation Support
Segmentation redesign, secure remote access, and log integration are complex projects that benefit from specialized expertise. Implementation services help ensure:
- Minimal downtime during deployment.
- Documentation that operations can maintain.
- Policy design that matches real plant workflows.
- Validation through testing and gradual enforcement.
Incident Response Planning & Exercises
Mature manufacturers plan for incidents as a certainty, not a possibility. Incident response services should include:
- OT-aware playbooks that clarify when to isolate networks, how to preserve safety, and who decides.
- Tabletop exercises involving operations, engineering, IT, and leadership.
- Forensics readiness (logging, retention, evidence handling) that speeds investigations and insurance claims.
Continuous Governance & Program Management
Cyber maturity improves when the program is owned end-to-end. For many manufacturers, that means a combination of internal leadership and external support to keep momentum. Governance services may include:
- Policy and standards for OT security, remote access, and change control.
- Risk register management with documented decisions and exception tracking.
- Metrics that leadership can understand (coverage, exposure, time-to-detect, time-to-contain, restore success rate).
How to Choose the Right Tools: A Practical Evaluation Framework
With so many vendors and overlapping claims, selecting manufacturing cybersecurity tools can feel overwhelming. Here’s a practical framework that keeps you focused on operational outcomes rather than feature lists.
1) Start With Your Highest-Impact Risks
Ask: What incidents would most disrupt production or create safety/quality consequences? Common answers include ransomware affecting plant servers, compromised remote access, and uncontrolled lateral movement between zones. Let these risks drive tool priorities.
2) Validate OT Compatibility and Operational Safety
OT environments require tools that won’t destabilize systems. Evaluate:
- Does the tool support passive monitoring where needed?
- Has it been validated for industrial protocols and common OT architectures?
- Can it run safely on OT-adjacent Windows systems without interfering with operations?
- Does the vendor understand maintenance windows and plant constraints?
3) Prioritize Integration Over “Another Dashboard”
Mature programs reduce complexity. Favor tools that integrate into your incident response workflow: SIEM, ticketing, identity, and OT monitoring should connect so you can investigate quickly and respond consistently.
4) Consider Total Cost of Ownership (People + Process)
The tool cost is only part of the equation. Ask:
- Who will manage and tune this tool weekly?
- What skills are required—OT engineering, IT security, both?
- Does a managed service (MDR/SOC) make more sense than building in-house coverage?
5) Measure Maturity Gains With Simple Metrics
Cyber maturity should show progress. Start with metrics like:
- Asset coverage: percent of OT/IT assets accurately inventoried.
- Segmentation maturity: number of zones with enforced policy and monitored chokepoints.
- Vulnerability reduction: time-to-remediate for critical exposures and tracked exceptions.
- Response readiness: time-to-detect, time-to-contain, and restore test success rates.
Common Pitfalls That Stall Cyber Maturity
Many manufacturers invest in security but don’t see maturity gains because their programs stall in predictable ways. Watch for these patterns:
- Tool sprawl without ownership: platforms are deployed but not tuned, integrated, or maintained.
- Flat networks: the environment remains highly connected, allowing threats to spread quickly.
- Vendor access “exceptions”: always-on VPNs and shared credentials become permanent.
- Patching paralysis: fear of downtime leads to unmanaged exposure and no compensating controls.
- No exercises: plans exist on paper, but teams haven’t practiced response or recovery.
The best way to avoid these pitfalls is to run cyber maturity as a program: align leadership, map risks to controls, implement in phases, and measure progress.
Putting It Together: A 90-Day Path to Stronger Manufacturing Cyber Maturity
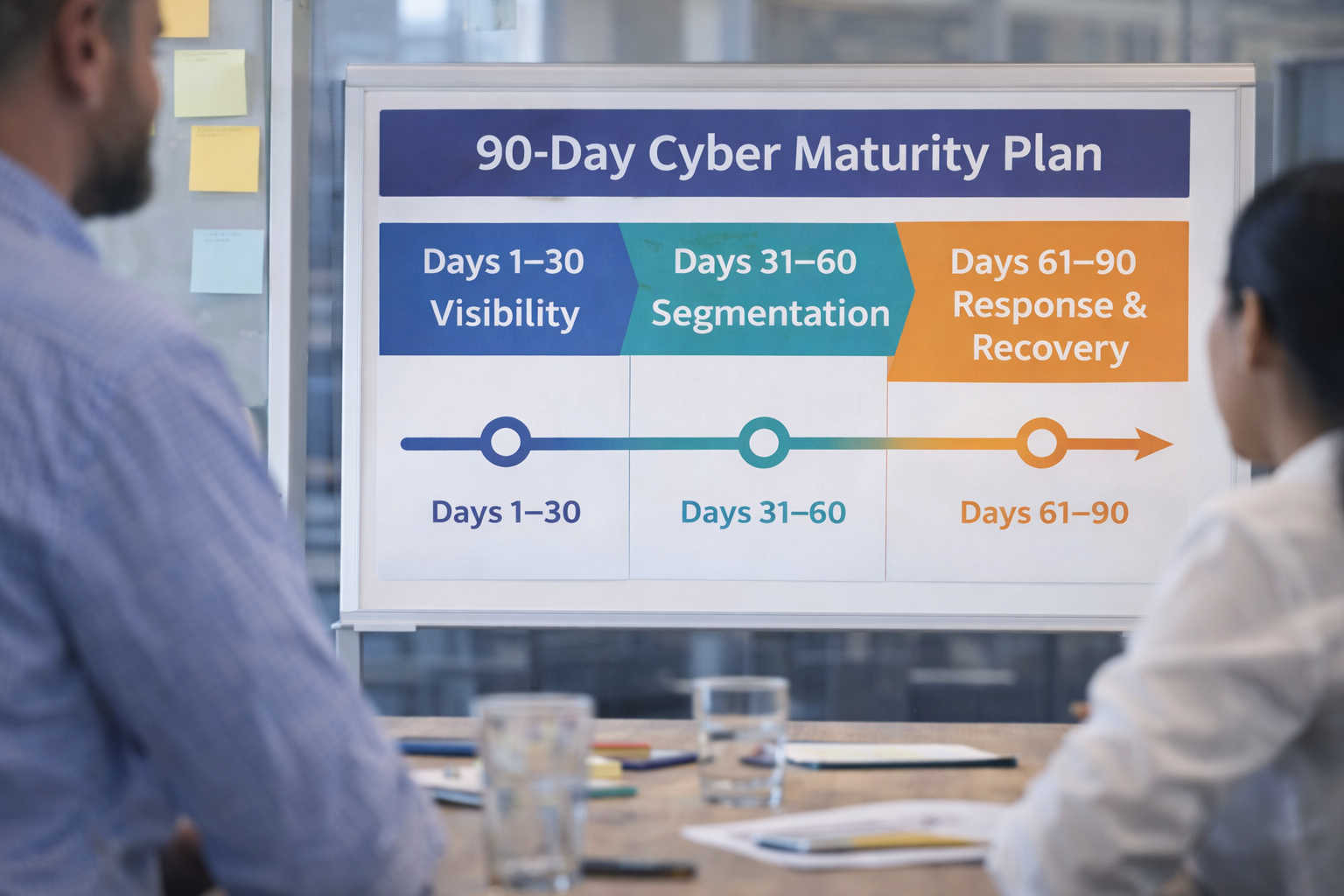
If you want a realistic starting plan, here’s a 90-day approach that many manufacturers can execute without halting production. The exact plan depends on plant complexity and existing controls, but this framework can quickly build momentum.
Days 1–30: Visibility & Risk Alignment
- Establish a joint IT/OT security working group (operations, engineering, IT, leadership sponsor).
- Deploy or expand OT visibility in key zones to identify assets and communications.
- Inventory remote access paths, vendor accounts, and critical “bridge” systems (DMZ/jump servers).
- Document the top operational risks and define “what must stay running” systems.
Days 31–60: Segmentation & Vendor Access Control
- Implement or tighten a DMZ architecture and define clear IT/OT boundaries.
- Restrict vendor access with MFA, approvals, and session monitoring.
- Begin staged enforcement of segmentation rules (monitoring first, blocking later).
- Centralize logging for high-value systems and integrate OT monitoring alerts into the workflow.
Days 61–90: Patch Governance & Response Readiness
- Launch an OT-aware patch management process with prioritization and exception tracking.
- Harden critical endpoints (EDR where validated, allowlisting on high-value systems).
- Run an incident response tabletop exercise that includes operations and engineering.
- Perform a restore test for key systems and validate backup integrity.
This approach doesn’t require perfection. It creates a measurable shift toward maturity: improved visibility, tighter access controls, reduced lateral movement, and a real ability to respond when issues arise.
How Cyber Advisors Helps Manufacturers Achieve Cyber Maturity
Cyber maturity is not just about selecting the “right” product—it’s about aligning tools, services, and operational realities into a program that reduces risk while supporting uptime. Cyber Advisors helps manufacturers do this by combining IT and OT expertise into a practical roadmap and implementation plan.
Where We Typically Start
- OT/IT cyber maturity assessment aligned to your operational risks and business goals.
- SCADA/ICS security strategy to improve visibility and detection without disrupting production.
- Network segmentation planning to control lateral movement and reduce incident impact.
- Vendor risk and remote access governance are built around least privilege and auditability.
- OT-aware patch management with prioritization, scheduling, and compensating controls.
Ready to Build a Practical OT/IT Cyber Maturity Roadmap?
If you’re working to improve manufacturing cybersecurity tools and OT security services coverage—but need a clear, operationally safe plan—Cyber Advisors can help.
- Identify the highest-impact gaps across SCADA/ICS, segmentation, vendor access, and patch management
- Prioritize investments that reduce operational risk fastest
- Implement controls with minimal downtime and clear ownership